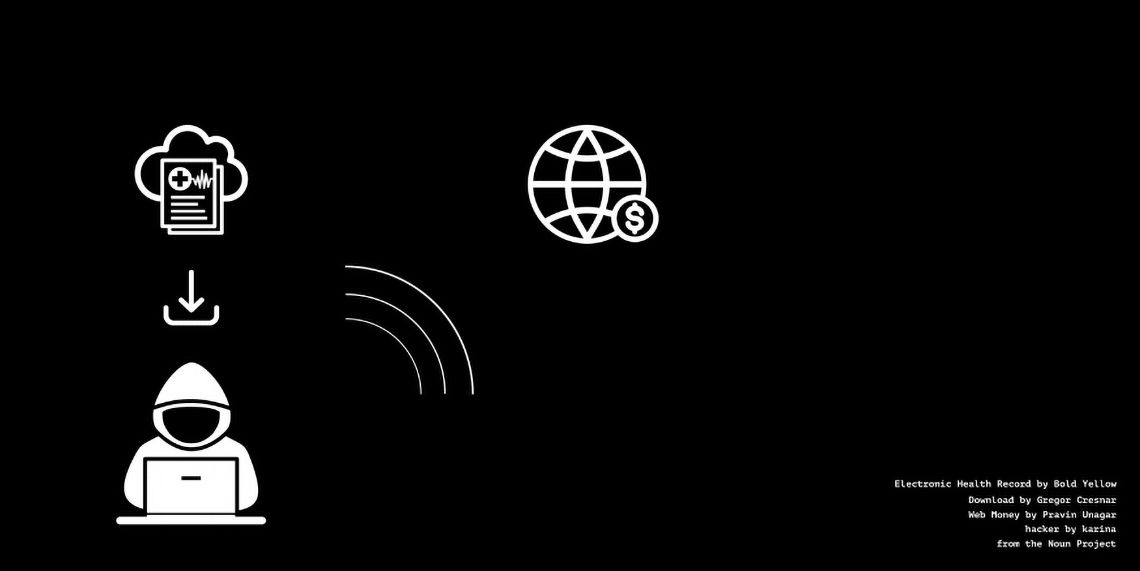
Imagine receiving a phone call or email notifying you that your most personal information such as your medical history, medications, social security number and much more has been stolen. Now imagine you are only one of 79 million people who received this notification. This scenario is not hypothetical; it was the largest medical data breach to date. In 2014, the health insurance company Anthem suffered a massive cybersecurity attack, compromising the health information of millions of individuals(1). Five years after this cyberattack, two Chinese nationals were finally charged by the Justice Department as conspirators in this cyberattack, which resulted in an incredible $115 million in damages being paid out to the victims(1). More recently, in May of 2019, the American Medical Collection Agency (AMCA) notified the medical testing company, Quest Diagnostics, of a potential breach which culminated in a verified 11.9 million patients’ data being compromised including financial information, social security numbers, and medical data (1). Addressing the rise of cyber attacks in healthcare, Vice President of Worldwide Sales for the cloud and data security company nCipher Security, Peter Carlisle claimed, “Healthcare organizations collect and store vast amounts of personal information, making them a major target for cyber-criminals. This valuable data can be used for identity theft(2)."
Moreover, while these cyber-attacks necessitate better cybersecurity, the amount of protected health information (PHI) in circulation with third-party vendors only serves to increase the risk of medical and financial data breaches. PHI can be any personally identifying information such as one’s full name, social security number, medical history, and even full-face photos, to name a few. In the Health Insurance Portability and Accountability Act (HIPAA) of 1996, data privacy and security provisions were put in place to safeguard medical information, forming a legal basis for PHI. Under HIPAA, named data is governed and protected, and it must be made anonymous with easily identifiable information being removed before information is exchanged with outside parties(3). However, according to Harvard University fellow, Adam Tanner, there is not always much protection of one’s information. Tanner claims, “It's as though I had a picture of you naked and cut off the head and then sold the picture of your body to someone else(3)." Many theorize that state actors are buying this patient medical health information and potentially looking to utilize it to create profiles of Americans in addition to looking for high-value targets. These individuals are referred to as “data miners,” who collect, sell and barter anonymized, yet intimate, details of patient data(4).
Shockingly, even children’s medical health records have become a commodity on the dark web with some sellers disclosing PHI as well as the instructions on methods of extortion from the child’s parents after illegally acquiring data from pediatricians’ databases(5). Healthcare PHI has become one of the most valuable commodities on the dark web, more so than credit card information or social security numbers alone. Patient records can be sold by these “data miners” for up to $1,000 based on the information acquired while individually social security numbers and credit card information can be purchased for $1 and $110, respectively(6). Frequently, this PHI is sold in bundles called “Fullz,” which are records of structured PHI designed for the purpose of being sold and utilized for extortion and/or fraud(5).
In summation, the health care sector has many protections for patients; however, even with these protections afforded by HIPAA there still exist loopholes for third party vendors to acquire anonymized, yet intimate, protected health information. Consequently, cyber criminals can utilize this to their advantage to harness control of patient personal data for means of financial extortion as well as fraud, resulting in reputational repercussions as well as up to millions of dollars in financial settlements for healthcare providers and third-party vendors, such as insurance companies. In the coming weeks, we will expound upon how in the midst of a global pandemic, hackers are utilizing fear and discord to take advantage of our healthcare system.
References:
- Rowland, Christopher. (2019, Jun. 3). Quest Diagnostics Discloses Breach of Patient Records. Retrieved from https://www.washingtonpost.com/business/economy/quest-diagnostics-discloses-breach-of-patient-records/2019/06/03/aa37b556-860a-11e9-a870-b9c411dc4312_story.html.
- O’ Flaherty, Kate. (2018, Oct. 5). Why Cyber-Criminals Are Attacking Healthcare -- And How To Stop Them. Retrieved from https://www.forbes.com/sites/kateoflahertyuk/2018/10/05/why-cyber-criminals-are-attacking-healthcare-and-how-to-stop-them/#3a4f183d7f69.
- Noman, Natasha. (2017, Jan. 12). Companies are Making Billions Off Your Medical Data – and You Won’t Get a Cent of It. Retrieved from https://www.mic.com/articles/165093/companies-are-making-billions-off-your-medical-data-and-you-wont-get-a-cent-of-it.
- Tanner, Adam. (2017, Jan. 10). Strengthening Protection of Patient Medical Data. Retrieved from https://tcf.org/content/report/strengthening-protection-patient-medical-data/
- Cynerio Research. (2018, Jun. 11). Healthcare Hacking Trends on the Dark Web. Retrieved from https://www.cynerio.com/blog/healthcare-hacking-trends-on-the-dark-web.
- Garrity, Mackenzie. (2019, Feb. 20). Patient Medical Records Sell for $1K on Dark Web. Retrieved from https://www.beckershospitalreview.com/cybersecurity/patient-medical-records-sell-for-1k-on-dark-web.html.

Justin Hull is a research fellow for Urgent Matters. A graduate in neuroscience from George Mason University. He is a medical scribe at George Washington Hospital while studying to get into medical school and has also scribed at Inova Fairfax Hospital ED.

Jordan Selzer is a Disaster and Operational Medicine Fellow and Emergency Medicine Physician at George Washington University. His areas of focus include operationally focused disaster response work as well as healthcare cybersecurity. He has significant disaster response experience: having worked in the US Virgin Islands after Hurricanes Irma and Maria as well as the Bahamas after Hurricane Dorian. His cybersecurity work has included collaborating with FDA regulators, FBI cybersecurity experts, and medical device security researchers. He is also a co-founder of an app-based medical tech startup MayJuun, focused on improving physician experience of healthcare delivery.
Dr. Selzer attended medical school at Loyola University Chicago and completed his residency in Emergency Medicine at Maricopa Medical Center in Phoenix, Arizona. He is currently pursuing a Master in Public Health degree from George Washington University with a focus in Humanitarian Health and Emergency Management.